Why is this interesting? - The Security Edition
On scams, passwords, and the security anti-patterns that do more harm than good
Noah here. For years now I’ve been railing against banks and credit card companies who call you up, inform you of potential fraud, and then ask for your card number to confirm your identity. The danger in the practice is that they train people to feel confident giving a random caller secure bits of information just because they claim to be who they say they are. I’ve been waiting to hear of an example of someone taking advantage of this behavior, and Tuesday on Twitter I saw exactly that by way of a very interesting thread from Pieter Gunst, a lawyer and co-founder of a company called Legal.io:
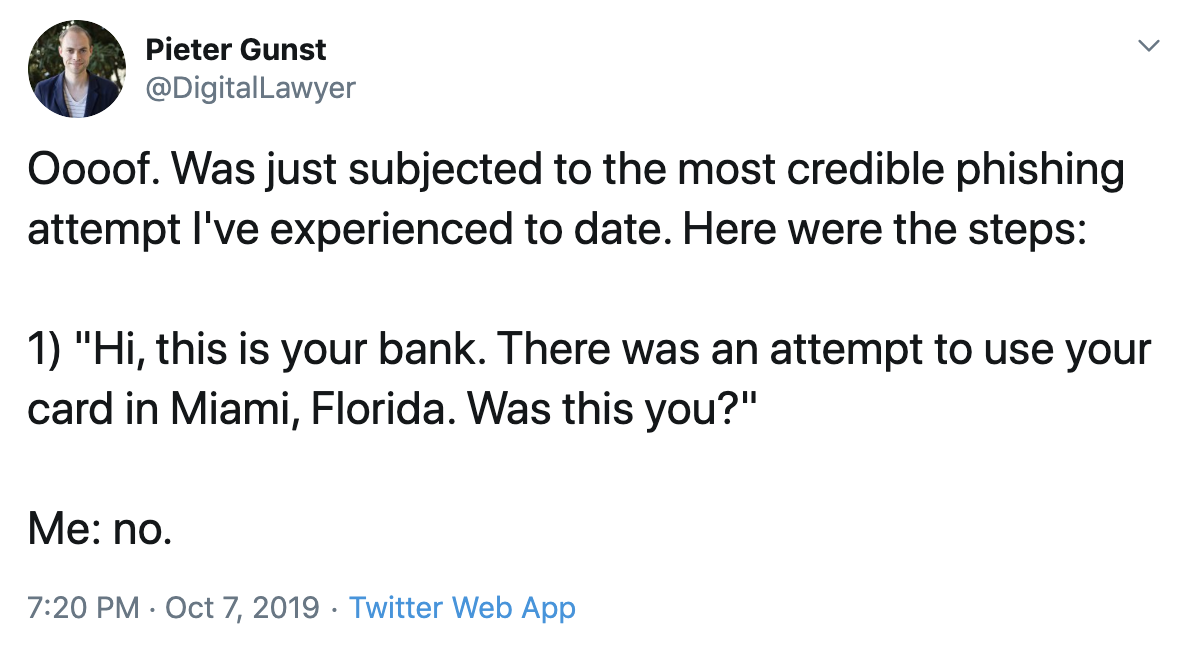
He goes on to explain that the bank’s phone number had been spoofed and that the scammer sent him a real text message code (using a password reset flow from the bank’s site). He was going along until they eventually asked for his pin, which is when he figured out what was going on.
Why is this interesting?
This was all possible thanks to something the software industry calls an “anti-pattern”. First coined in the mid-90s, an anti-pattern is essentially a solution that seems reasonable, but does more harm than good (and there’s a better alternative). “An antipattern is just like a pattern, except that instead of a solution it gives something that looks superficially like a solution but isn't one,” is how computer scientist Andrew Koenig described it in the original paper. (I’ve sadly not been able to turn up a copy of that paper despite a good amount of searching, so I’m relying on secondhand information.) In this case, the anti-pattern is calling people and asking them to confirm their identity instead of simply asking them to call the number on the back of their card (since in most cases these days the fraud is digital not physical).
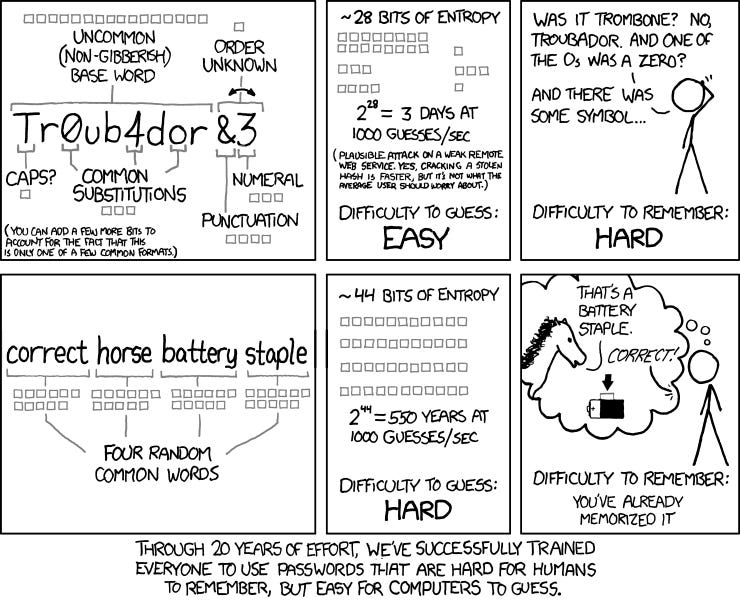
That’s not the only anti-pattern in security, though. There are lots of other terrible approaches that we’re bombarded with every day that act to make us less secure over time. There’s the one where the Apple password prompt randomly pops up in a different app, making you feel comfortable typing your iCloud password into any old screen. And, of course, there’s the widespread use of overly complicated password rules. Requiring you to include 2 letters, a number, and three punctuation marks only act to make it more likely that you’ll either have to re-use passwords or leave a copy in your desk drawer (until everyone uses password managers like 1Password that is). What’s the better alternative? Here’s the XKCD answer:
The reality is that in almost all security, humans are the biggest weakness. That’s why phishing (and now spear-phishing where you write much more targeted emails to higher potential targets) is so effective: People are easily tricked with just a bit of plausible information. Just the other day I caught myself replying to an email asking for some login details. The sender was a friend and the request plausible, but as soon as I hit send on the reply I realized I didn’t double-check to make sure it was really him. I quickly texted and it turned out it was, but it could have just as easily been someone targeting me.
While I would hope that institutions would start getting a lot more savvy about this stuff and stop lulling people into a false sense of security, I’m not holding my breath. In the meantime, my security bundle includes a password manager (I’m partial to 1Password, but as long as it’s a reputable one you will be good), turning on two-factor authentication wherever possible (using my device, not SMS, which can be susceptible to porting), and hardware keys in a few places that I want to be extra safe (they’re just a second-factor that you need to have in your possession). Beyond that, I don’t tell anyone the very few passwords I do know (not even my family), I’m very careful about what applications I give Oauth access to, and I try to keep myself skeptical of any calls, emails, or physical mail that asks for personal information. No system is perfect, though, and I assume at some point I’ll slip, which is why I make sure the extra important stuff, like the email everything is tied to, is even more secure.
But don’t trust me, listen to folks like Bruce Schneier instead. And then … cross your fingers. (NRB)
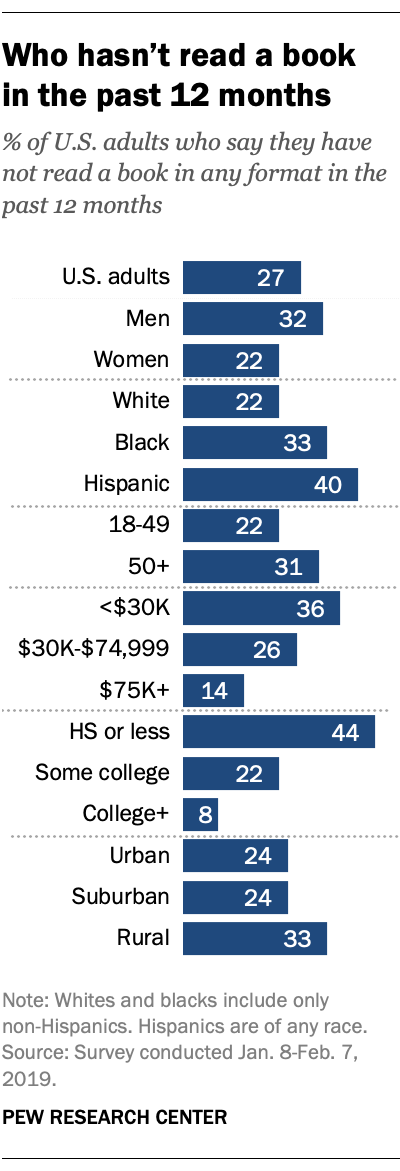
Chart of the Day:
From Pew, the percentage of US adults who haven’t read a book in the last twelve months. (NRB)
Quick Links:
There’s been some interesting research on the effect of C-sections on the microbiomes of babies. The impact isn’t fully understood yet and the advice on how to deal with it is still going back and forth, but a new study out of the UK (the largest to date) has shown “the strongest evidence yet that children born through the vaginal canal carry different microbes from those delivered by caesarean section. Newborns delivered by c-section, the study found, tend to lack strains of gut bacteria found in healthy children and adults. Instead, their guts harbour harmful microbes that are common in hospitals.” (NRB)
The FT’s Jo Ellison on the Wing opening in London. (CJN)
Thanks for reading,
Noah (NRB) & Colin (CJN) & Felix (FMS)
Why is this interesting? is a daily email from Noah Brier & Colin Nagy (and friends!) about interesting things. If you’ve enjoyed this edition, please consider forwarding it to a friend. If you’re reading it for the first time, consider subscribing (it’s free!).


